Insomni’hack 2025 — Forensic Write up — TheQuietFruit
Hello everyone! Today we are going to make the report of the forensic challenge TheQuietFruit that was published during the Insomni’hack 2025 !
The flag has been split into 3 parts that need to be found.
When we have downloaded the file, we see a .zip file that can be unpacked with the use of :
1
unzip TheQuietFruit.zip
We get a folder with an NTFS architecture.
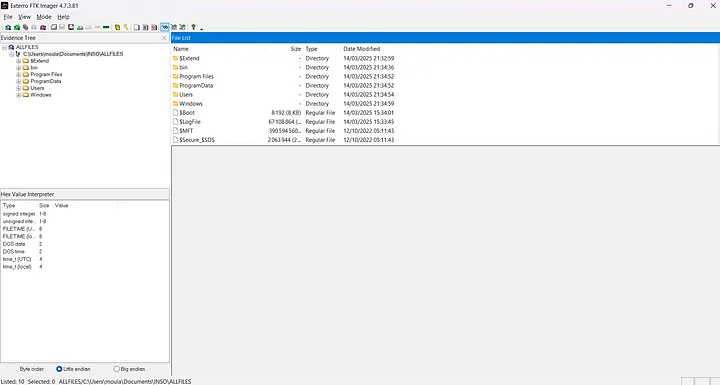
Then we need to view it on a tool that allows us to navigate and view the contents easily so as not to lose time. FTK Imager is the one that I use thanks to a facility of use.
Once the file is exported to FTK Imager, we have the complete arborescence of the folder in our visualisation.
The first flag
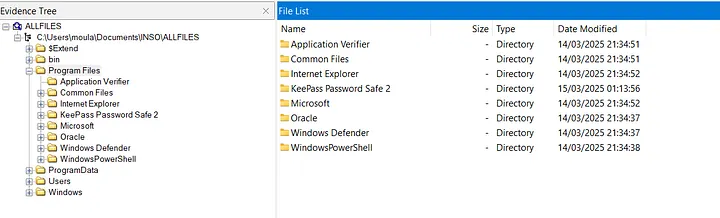
On the first analysis of the installed software, we see a file called “KeePass Password Safe 2”, which is a software to keep our password safe ;)
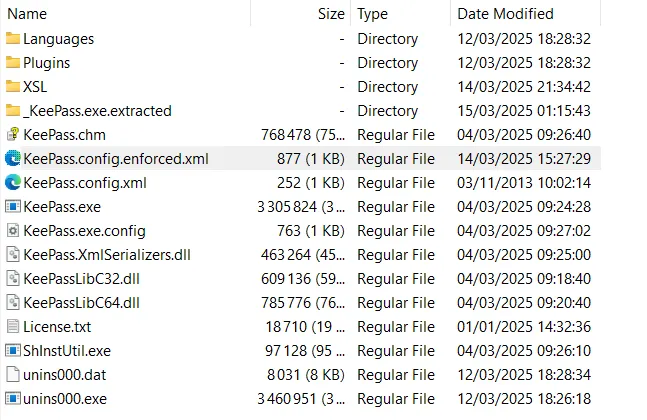
There is an overview of the KeePass folder files:
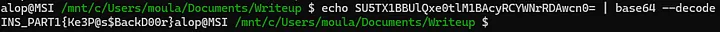
By quickly checking the whole file, we see in “KeePass.config.enforced.xml” that there is a base64 encoded string
By decoding it, we got the first flag!
And there it is !
- INS_PART1{Ke3P@s$BackD00r}
The second flag
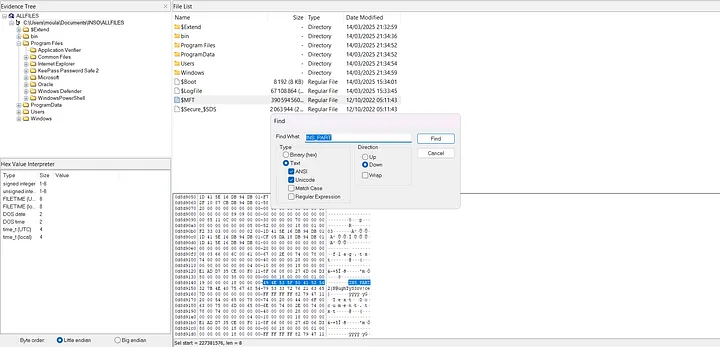
The second flag is in the MFT table. There is a system of stored files in it if they have a size that is less than 1024 octets. The content is stored directly in the MFT. When we check this, we see that we can get the flag directly by doing a simple FIND.
There is the flag
- INS_PART2{N@ughTyS3rv!ce}
The third flag
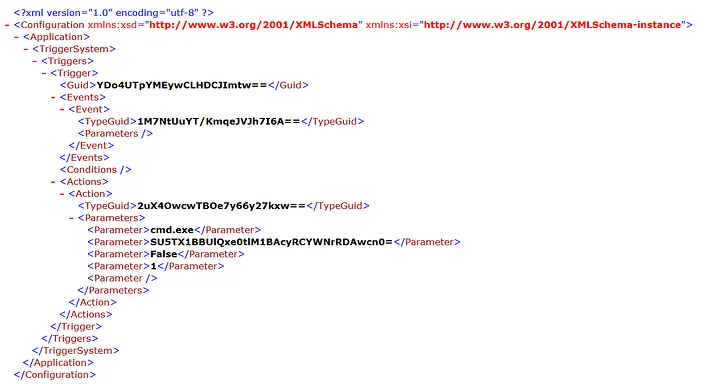
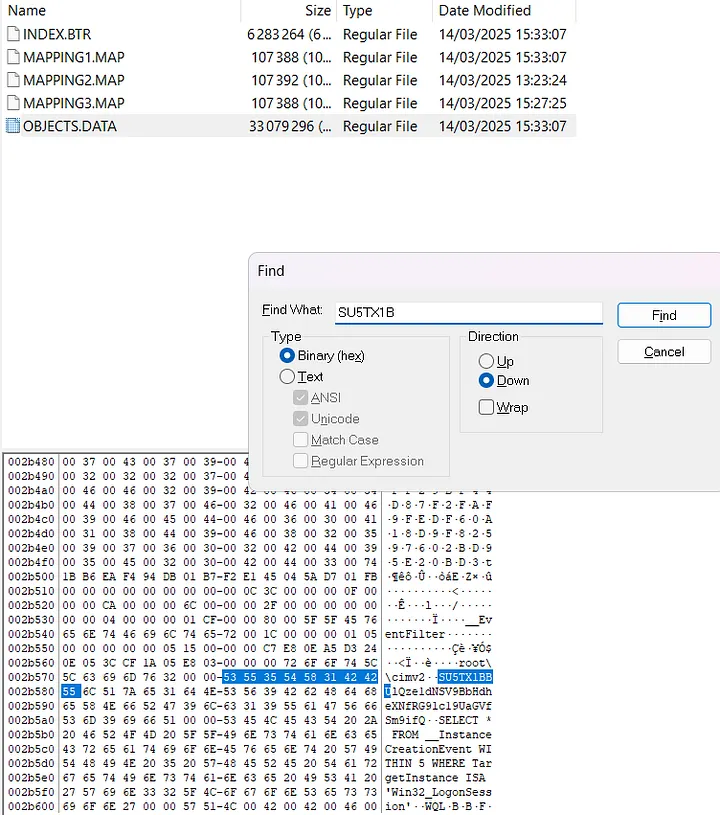
To get the third flag, we need to look in the OBJECT.DATA file. This repository contains scripts used to find evidence in WMI (Windows Management Instrumentation) repositories.
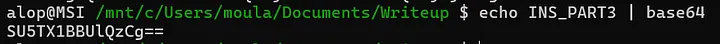
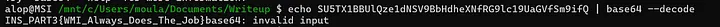
To get the flag, we had to encode the known part of the flag “INS_PART3” and look in OBJECT.DATA to get the encoded file.
And there is the flag !
- INS_PART3{WMI_Always_Does_The_Job}
Finally, the challenge was broken down into 3 flags to find in an NTFS system. By checking software, MFT and WMI artefacts we were able to find the 3 flags:
- INS_PART1{Ke3P@s$BackD00r}
- INS_PART2{N@ughTyS3rv!ce}
- INS_PART3{WMI_Always_Does_The_Job} Thanks for reading this !